A small group of unauthorized users reportedly gained access to Anthropic’s Claude Mythos Preview through a third-party vendor environment, even though the company has said the model “poses unprecedented cybersecurity risks” and is not meant for broad release.
Bloomberg reported the access on April 21, 2026, and Anthropic says it is investigating with no evidence its own systems were impacted.
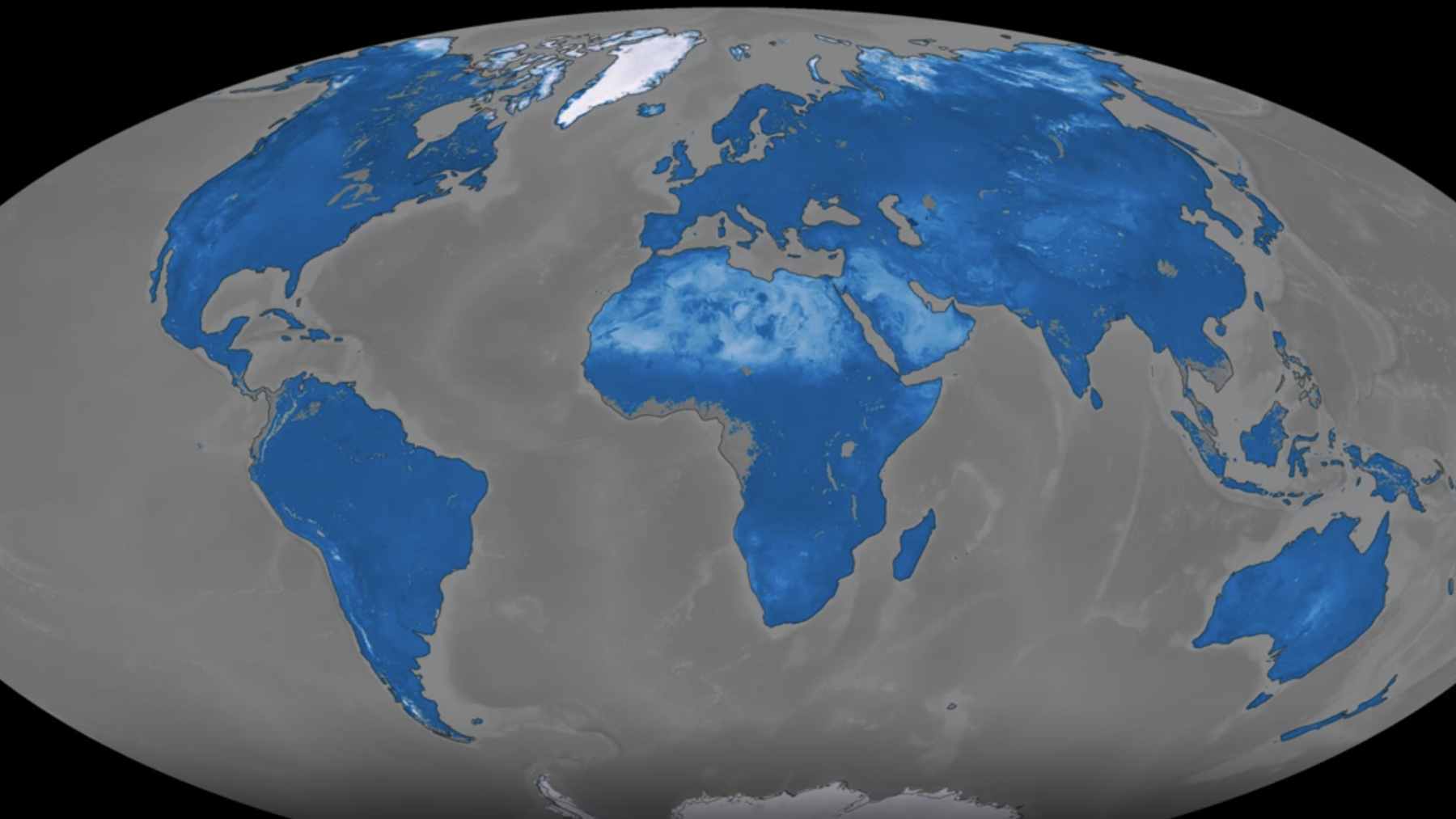
That might sound like a niche tech leak, but it lands on the same faultline as climate policy. Power grids, water plants, and renewables are becoming software-driven systems, and a cyber incident can ripple into real-world services fast.
What happens when the code that keeps the lights on meets an AI that can spot weaknesses at machine speed?
What happened with Mythos
Bloomberg reported that members of a Discord community looking for unreleased AI models accessed Mythos and then used it regularly, with the group described as non-malicious and driven largely by curiosity.
Anthropic confirmed it is investigating “unauthorised access to Claude Mythos Preview” through a third-party vendor environment.
The model is being tested under Project Glasswing, an Anthropic-led effort that pulls in heavyweight partners such as Amazon Web Services, Apple, Microsoft, and NVIDIA.
Anthropic says it is committing up to $100 million in usage credits for Mythos Preview and $4 million in donations to open-source security organizations. Anthropic says the model has found thousands of high-severity vulnerabilities across major operating systems and web browsers.
Why this matters for energy and water
The climate transition is wired. European Commission guidance puts it bluntly: as the energy system becomes more digital, exposure to cyber incidents can jeopardize the security of energy supply, while cross-border interconnections can turn one failure into a cascade.
Essentially, it is a giant software upgrade for the planet, and every upgrade brings bugs.
We have already seen how “just IT” incidents spill into the physical world. In Minot, North Dakota, a ransomware attack knocked a water treatment plant’s SCADA system offline and operators had to run manual processes, reading gauges for 16 hours while systems were rebuilt, serving around 80,000 users.
If you are wondering what this looks like at street level, think about the basics. Clean water and stable power matter most on the hottest days of the year, when the air conditioner is chewing through electricity and everyone is watching the electric bill.
The vulnerability gap is shrinking
Anthropic’s own security write-ups make clear why Mythos is treated as a “frontier” cyber tool. Its Red Team says the model can identify and exploit zero-day vulnerabilities across every major operating system and web browser when directed, and that it is capable enough that non-experts inside the company could request exploit searches overnight and wake up to working results.
The same post lays out hard numbers that should make any critical-infrastructure operator pause. In one benchmark tied to Firefox exploit development, Anthropic reports Mythos produced working exploits 181 times, and in its OSS-Fuzz-style testing it achieved full control-flow hijack on ten fully patched targets.
That capability collides with an uncomfortable reality in renewable energy hardware. A Forescout analysis highlighted nearly 35,000 internet-exposed solar power devices, and it warned that outdated firmware and weak configurations can turn “small” devices like inverters or gateways into entry points toward larger systems.
Business and defense are now tied to the same risk
For companies, this is no longer a compliance checkbox. Trustwave’s 2025 deep dive on ransomware in energy and utilities tracked attacks claimed on extortion sites rising sharply into 2023 and 2024, with the United States accounting for 47% of the sector’s targeted victims in its dataset.
The operational stakes can also be huge. In one example highlighted in the same report, a ransomware group claimed control over systems tied to a gas storage facility with a reported capacity of 750 million cubic meters, and Trustwave noted that even a smaller shortage could translate into days of lost supply in major markets during winter.
Governments are treating these threats as national security, especially as renewables scale.
Poland’s energy minister said the country’s cyberspace forces diagnosed its strongest attack on energy infrastructure in years, aimed at disrupting communication between renewable installations and distribution operators, and Japan has announced a financial sector task force amid fears that AI-enabled cyber tools could outpace patching defenses.
What to watch next
The Mythos incident is also a supply chain lesson, because the reported access route ran through a third party. For climate tech and utilities, that is a reminder to look past the core platform and audit the vendor tooling around it, including identity controls, logging, and how test environments are separated from anything that can touch production systems.
There is a more optimistic read, too. Anthropic argues that the same AI capabilities that could speed up attacks can also help defenders find and fix bugs faster, and Project Glasswing is built around sharing what is learned so partners and open-source maintainers can patch before exploits spread.
At the end of the day, the environment angle is simple. A cleaner economy depends on more connected infrastructure, and that makes cybersecurity part of climate resilience, whether we talk about solar inverters, water pumps, or the grid control rooms you never see.
The official technical assessment was published on red.anthropic.com.